I've used both SQLite browser and DBeaver (and more). I've used SQLite, PostgreSQL, Oracle, and SQL Server databases. Creating an ERD in DBeaverLocation of SQL and Data: https://app.box.com/s/expnupayh74vt3fo888vab9qjjhxddln. Download DBeaver for Windows PC from FileHorse. 100% Safe and Secure ✔ Free Download (32-bit/64-bit) Latest Version 2021. From a Dbeaver issue on github, it's not possible. Serge-rider commented on Nov 18, 2019 You cannot use SSH with SQLite. SQLite is embedded database, there is no such thing as SQLite server.
1.0 Introduction
This file describes the SQLite Encryption Extension (SEE) forSQLite. The SEE allows SQLite to read and write encrypteddatabase files. All database content, including the metadata, isencrypted so that to an outside observer the database appears tobe white noise.
A version of SQLite that includes SEE is also able to read andwrite normal database files created with a public domain versionof SQLite. But the public version of SQLite will not be ableto read or write an encrypted database file. Indeed, no versionof any known software will be able to access an encrypteddatabase file without knowing the encryption key.
The SEE is actually a set of extensions employing various encryption algorithms. The following encryption algorithms arecurrently supported:
- AES-256 in OFB mode (recommended for all new development)
- AES-128 in OFB mode
- AES-128 in CCM mode
- RC4 with security enhancements (legacy only)
2.0 License
The core SQLite library is in the public domain. However, the extensionsneeded to read and write an encrypted database file are licensedsoftware. You should only be able to see this software if you havea license.
Your license is perpetual. You have paid a one-time fee that allows youto use and modify the software forever. You can ship as many copied ofthe software to your customers as you want so long as you ensure thatonly compiled binaries are shipped (you cannot distribute source code)and that your customers cannot make additional copies of the software to use for other purposes.
You can create multiple products that use this software as longas all products are developed and maintained by the same team.For the purposes of this paragraph, a 'team' is a work unit whereeverybody knows each others names. If you are in a large companywhere this product is used by multiple teams, then each team shouldacquire their own separate license, or an enterprise license.
3.0 How To Compile
Your application sees SEE as a single large file of C-code that is adrop-in replacement for the SQLite amalgamation. The SEEsource-code file works and compiles just like the public-domain 'sqlite3.c'amalgamation. If you already build your application using thepublic-domain 'sqlite3.c' file, then to build using SEE you merelyreplace the public-domain 'sqlite3.c' with an SEE-enabled 'sqlite3.c'file and recompile.
There are nine different SEE-enabled 'sqlite3.c' files to choose from:
- sqlite3-see-aes256-openssl.c
- sqlite3-see-aes256-cryptoapi.c
- sqlite3-see-aes256-ofb.c
- sqlite3-see-cccrypt.c
- sqlite3-see-aes128-ofb.c
- sqlite3-see-aes128-ccm.c
- sqlite3-see.c
- sqlite3-rc4.c
- sqlite3-xor.c
The recommended procedure for adding SEE into your application is to copyone of these files into your application source tree, renaming it as 'sqlite3.c' and overwriting the public-domain 'sqlite3.c' source file,then recompile. After recompiling, your application should continue workingexactly as it did before, reading and writing ordinary unencrypted SQLitedatabases. Once you have recompiled and verified that everything stillworks, then go back in and add a PRAGMA (described below) that activatesencryption to your application code, and you are done.
3.1 Source Code Files In The SEE Distribution
The following are the source-code files used to implementthe SQLite Encryption Extension:
This file is a drop-in replacement for the public-domain 'sqlite3.c' file, adding support for encryption using the AES-256 in OFB mode by linking against the external OpenSSL library.
This file is a drop-in replacement for the public-domain 'sqlite3.c' source file, adding encryption capabilities using the AES256 in OFB mode using the CryptoAPI native interface on Windows.
This file is a drop-in replacement for the public-domain 'sqlite3.c' file, adding support for encryption using the AES-256 in OFB mode using a built-in copy of the Rijndaal reference implementation.
This file is a drop-in replacement for the public-domain 'sqlite3.c' filef, adding support for the AES-128 and AES-256 encryption algorithms, in OFB mode, using the external CCCrypt encryption. CCCrypt is the default encryption library on MacOS and iOS, and so this implementation of SEE is recommended for those platforms.
The see-ccrypt.c module normally only does AES128 encryption. However, when see-cccrypt is compiled with -DCCCRYPT256, it will use AES256 if and only if the key is exactly 32 bytes long.
This file is a drop-in replacement for the public-domain 'sqlite3.c' file. This replacement adds support for the AES-128 encryption algorithm in OFB mode using the Rijndaal reference implementation.
This file is a drop-in replacement for the public-domain 'sqlite3.c' file. This replacement adds support for the AES-128 encryption algorithm in CCM mode. CCM mode includes a message authentication code which provides authentication in addition to confidentiality. This uses the Rijndaal reference implementation for AES.
This file is a drop-in replacement for the public-domain 'sqlite3.c' file, adding support for encryption using the RC4 algorithm. RC4 is no longer considered secure. You should not use this implementation of SEE. It is provided for historical compatibility only.
This file is a drop-in replacement for the public-domain 'sqlite3.c' source file, adding support for encryption using any of the RC4, AES128-OFB, or AES258-OFB algorithms. The algorithm used is based on a prefix to the encryption key. If the key material begins with 'rc4:' then RC4 encryption is used. If the key material begins with 'aes128:' then AES128-OFB is used. If the key material begins with 'aes256:' then AES256-OFB is used. If none of these three valid prefixes appear on the key, then AES128-OFB is the default algorithm. A valid prefix is removed from the key prior to being passed on to the encryption algorithm.
This file is a drop-in replacement for the public-domain 'sqlite3.c' source file, adding pseudo-encryption which does nothing more than XOR the database against a repeated copy of the encryption key. This variant of SEE does not provide true encryption. It is for demonstration use only, or for use in cases where it is desirable to obfuscate a database file without actually encrypting it, perhaps due to legal constraints.
A copy of ordinary, unencrypted SQLite that contains additional hooks needed to add encryption. The other encrypted SQLite modules above are all copies of this file with additional code prepended and appended to do the encryption work. This file is provided for reference only and is probably not useful for development.
This file contains the interface definitions for SQLite. Other programs that link against SQLite will need this file, and you will need this file in order to compile the CLI, but you do not need this file to compile SQLite itself.
This file contains source code for the 'CLI', the Command Line Interface program named 'sqlite3.exe' that you can use to access and control SQLite database files. This file is different from the 'shell.c' file that comes with the public-domain version of SQLite. This shell.c has been enhanced to make use of the encryption extension.
3.2 Building And Compiling The SEE Code
To compile SEE into a static library, select an appropriate'sqlite3-see-*.c' source file (containing the algorithmand implementation you desire), then compile that filejust like you would compile anordinary public-domain 'sqlite3.c' source file. On unix systems,the command sequence would be something like this:
On windows, the commands are more like this:
3.3 Building A Shared-Library Or DLL
We encourage you to statically link SQLite against yourapplication. However, if you must use SQLite as a separate DLL orshared library, you can compile as follows on Linux:
Or on Windows:
3.4 Building The Command-Line Shell Program
To compile the CLI, just hand the shell.c source file to yourC compiler together with either the static library preparedabove, or the original source code files. A typical command onLinux is:
On a Mac:
On Windows with MSVC:
For an added performance boost when building the CLI, consideradding the -DSQLITE_THREADSAFE=0 option. The CLI is singlethreaded and SQLite runs faster if it doesn't have to useits mutexes.
SEE can also be built for Windows Phone 8,UWP 10, and Android.
4.0 Command-Line Usage
The CLI is the sameCLI used by public-domain SQLitethough with enhancements to support encryption.There are new command-line options ('-key', '-hexkey', and '-textkey')for specifying the encryption key.Examples:
If the key is omitted or is an empty string no encryption is performed.
There are three different key formats. The first format (-key) takesthe key string and repeats it over and over until it exceeds the numberof bytes in the key of the underlying algorithm (16 bytes for AES128,32 bytes for AES256, or 256 bytes for RC4). It then truncates the resultto the algorithm key size. That approach limits the key space since itdoes not allow 0x00 bytes in the key. The second format (-hexkey)accepts the key as hexadecimal, so any key can be represented. If theprovided key is too long it is truncated. If the provided key is tooshorted, it is repeated to fill it out to the algorithm key length.The third format (-textkey) computes a strong hash on the input keymaterial and uses that hash to key the algorithm. The -textkey formatis recommended for new applications.
4.1 Changing the encryption key
The SEE-enabled CLI also includes newdot-commands'.rekey', '.hex-rekey', and '.text-rekey' for changing the encryption key:
The first argument is always the old password, in exactly the formatas it was supplied to the '-key', '-hexkey', or '-textkey' optionswhen the command-line tool was started. If the the database waspreviously unencrypted, use an empty string ' as the key. The2nd and 3rd arguments are the new encryption key. You mustenter the new key twice to check for typos - the rekey will notoccur unless both instances of the new key are the same. Toencrypt a previously unencrypted database, do this:
The VACUUM step is not required to enable encryption but it ishighly recommended. The VACUUM command ensures that every pageof the database file has a secure nonce.The VACUUM is only needed when an existing,non-empty database file is encrypted for the first time.
To decrypt a database do this:
The .rekey command only works with text keys. To rekey a databasethat contains a binary key use the '.hex-rekey' command instead.The .hex-rekey command works just like .rekey except the new key isentered as hexadecimal instead of text. The '.text-rekey' commandcomputes a hash of the NEW argument and uses that hash as the encryptionkey.
5.0 C Interface
If you deploy the SQLite encryption extension as a DLL or sharedlibrary then you must first activate the library by invoking:
The argument is your product activation key. The activation keyis available as plain-text in the source code so you can clearlysee what it is. The purpose of the activation key is to preventone of your customers from extracting the SQLite library and usingit separately from your application. Without knowledge of theactivation key, which only you should know, your users will beunable to access the encryption features.
If you are unable to invoke the C-interface to sqlite3_activate_see()(perhaps because you are accessing SQLite through a wrapper layer) thenyou can also alternatively activate the encryption features using a PRAGMA:
Use the sqlite3_open() API to open an encrypted databaseor any database that you want to rekey. Immediately afteropening, specify the key using sqlite3_key_v2():
If the pKey argument is NULL or nKey is 0, then thedatabase is assumed to be unencrypted. The nKey parameter canbe arbitrarily large, though only the first 256 bytes (RC4) or16 bytes (AES128) or 32 bytes (AES256) will be used. In SEEversions 3.15.0 and later, if nKeyis negative, then pKey is assumed to be a zero-terminated passphrasestring. In that case the passphrase is hashed and the hash isused as the key to AES algorithm. The passphrase itself is usedas the key for RC4.
CAUTION: The feature of using a passphrase hash when nKey<0was added in version 3.15.0. If you use nKey<0 in any SEE versionprior to 3.15.0, encryption will be silently disabled, just as if youhad set nKey=0.
The see-ccrypt.c module uses AES128 encryption by default.However, if see-ccrypt.c is compiled with -DCCCRYPT256 and ifthe sqlite3_key_v2() interface is called with nKey32, thenAES256 encryption is used instead.
If you specify an incorrect key, you will not get an error messageright away. But the first time you try to access the databaseyou will get an SQLITE_NOTADB error with a message of'file is encrypted or is not a database'.
The zDbName parameter specifies which ATTACH-ed database should getthe key. Usually this is 'main'. You can pass in a NULL pointer asan alias for 'main'. Unless you have a good reason to do otherwise,it is best to pass in a NULL pointer for the zDbName parameter.
You can change the key on a database using the sqlite3_rekey() routine:
A NULL key decrypts the database.
Rekeying requires that every page of the database file be read,decrypted, reencrypted with the new key, then written out again.Consequently, rekeying can take a long time on a larger database.
Most SEE variants allow you to encrypt an existing database thatwas created using the public domain version of SQLite. This isnot possible when using the authenticating version of the encryptionextension in see-aes128-ccm.c. If you do encrypt a database thatwas created with the public domain version of SQLite, no noncewill be used and the file will be vulnerable to a chosen-plaintextattach. If you call sqlite3_key_v2() immediately after sqlite3_open()when you are first creating the database, space will be reservedin the database for a nonce and the encryption will be much stronger.If you do not want to encrypt right away, call sqlite3_key_v2() anyway,with a NULL key, and the space for the nonce will be reserved in thedatabase even though no encryption is done initially.
A public domain version of the SQLite library can read and writean encrypted database with a NULL key. You only need the encryptionextension if the key is non-NULL.
6.0 Using the 'key' PRAGMA
As an alternative to calling sqlite3_key_v2() to set the decryptionkey for a database, you can invoke a pragma:
You must invoke this pragma before trying to do any other interaction with the database. The key pragma only works withstring keys. If you use a binary key, use the hexkey pragmainstead:
For the equivalent of the --textkey option, in which the textpassphrase is hashed to compute the actual encryption key, use:
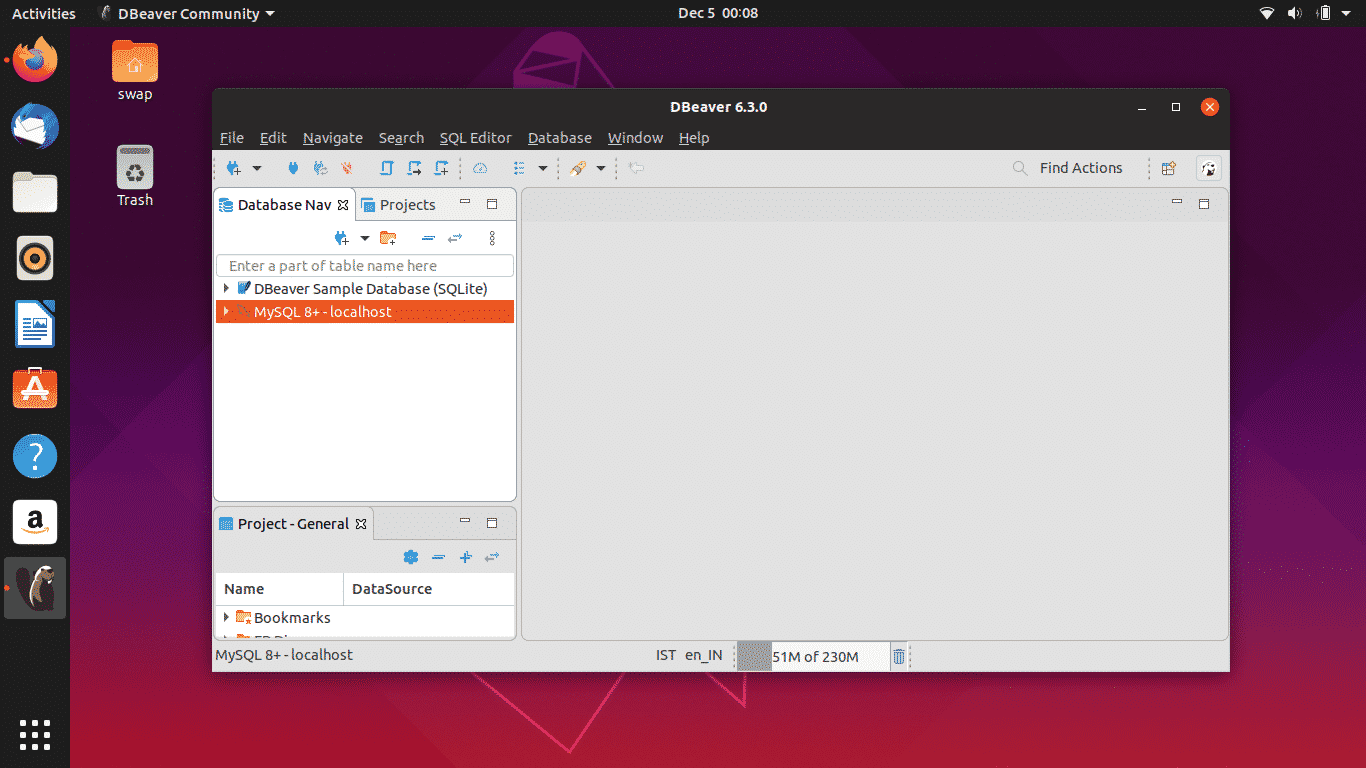
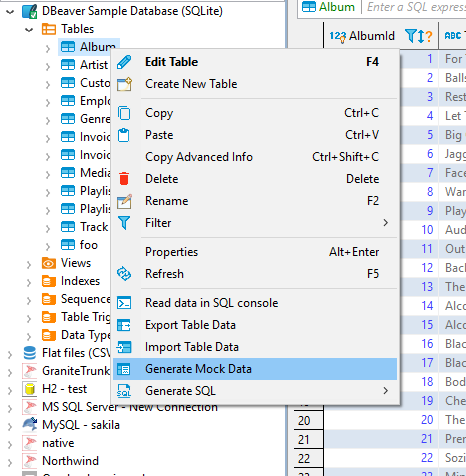
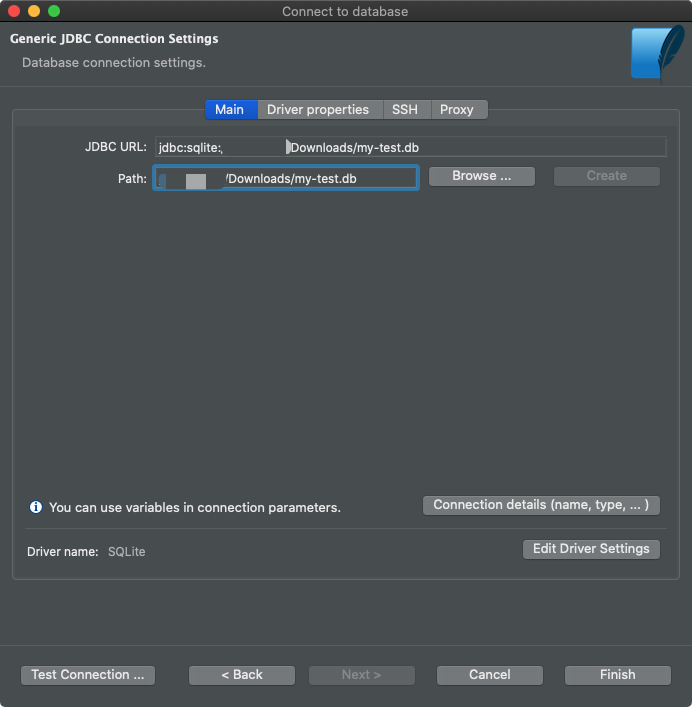
Sqlite Dbeaver Update
Use the rekey, hexrekey, or textrekey pragmas to change the key.So, for example, to change the key to 'demo2' use one of:
Through the use of these pragmas, it is never necessary to directlyinvoke the sqlite3_key_v2() or sqlite3_rekey_v2() interfaces. This meansthat SEE can be used with language wrappers that do not know aboutthose interfaces.
The 'key', 'hexkey', and 'textkey' PRAGMA statements expect the samekey strings as the '-key', '-hexkey', and '-textkey' argumentsto the command-line shell, respectively.
The key PRAGMAs will return a string 'ok' if they successfully loadan encryption key into SEE. If you invoke one of these pragmas ona system that does not support encryption, or if the key loadingoperation fails for any reason, then nothing is returned. Note thatthe 'ok' string is returned when any key is loaded, not necessarilythe correct key. The only way to determine if the key is correct isto try to read from the database file. An incorrect key will resultin a read error.
7.0 Using The ATTACH Command
The key for an attached database is specified using the KEY clauseat the end of the ATTACH statement. Like this:
If the KEY clause is omitted, the same key is used that is currentlyin use by the main database. If the attached database is notencrypted, specify an empty string as the key. The argument tothe KEY keyword can be BLOB constant. For example:
Using text as the KEY on an ATTACH statement expects the same key asone would provide to the '-key' option of the command-line shell. ABLOB value for KEY is means to use the same key as would have beenprovided by the '-hexkey' option to the command-line shell. There isno mechanism for specifying a passphrase to be hashed on an ATTACHstatement. If you are using a hashed key, you must compute the hashyourself and supply it as a BLOB.
8.0 Key Material
The amount of key material actually used by the encryption extensiondepends on which variant of SEE you are using. With see-rc4.c, thefirst 256 byte of key are used. With the see-aes128-ofb andand see-aes128-ccm variants, the first 16 bytes of the key are used.With see-aes256-ofb, the first 32 bytes of key are used.
If you specify a key that is shorter than the maximum key length, thenthe key material is repeated as many times as necessary to complete thekey. If you specify a key that is larger than the maximum key length,then the excess key material is silently ignored.
For the '-textkey' option, up to 256 bytes of the passphrase are hashedusing RC4 and the hash value becomes the encryption key.Note that in this context the RC4 algorithm is being used as a hashfunction, not as a cryptographic function, so the fact that RC4 isa cryptographically weak algorithm is irrelevant.
8.1 Encryption algorithm selection using a key prefix
For the 'sqlite3-see.c' SEE variant, the key may begin with a prefixto specify which algorithm to use. The prefix must be exactlyone of 'rc4:', 'aes128:', or 'aes256:'. The prefix is not used as part ofthe key sent into the encryption algorithm. So the real key shouldbegin on the first byte after the prefix. Take note of the followingimportant details:
The prefix is case sensitive. 'aes256:' is a valid prefix but 'AES256:' is not.
If the key prefix is omitted or misspelled, then the encryption algorithm defaults to 'aes128' and the misspelled prefix becomes part of the key.
The encryption algorithm can be changed using the sqlite3_rekey_v2() interface or the .rekey command-line. For example, to convert a legacy RC4-encrypted database to use AES-256, enter:
The algorithm prefix strings work on the 'sqlite-see.c' variant of SEE only. For any of SEE implementations, any prefix on the key is interpreted as part of the key.
The nKey parameter on sqlite3_key() and sqlite3_key_v2() must include the size of the prefix in addition to the size of the key.
When using PRAGMA hexkey or PRAGMA hexrekey, the key prefix must be hex encoded just like the rest of the key.
9.0 The Importance of a Nonce
The encryption is much more secure if it has a random nonce value oneach page of the database. Without a nonce, the encryption can be brokenusing a chosen-plaintext attack. Purists will argue (rightly) thatthe encryption is weak without a nonce.

The number of bytes of nonce on each page of the database is determinedby byte 20 of the database file. This value is set to zero by defaultin databases created by the public-domain version of SQLite. You can change this byte to a positive value by running theVACUUM commandusing an SEE-enabled version of SQLite.
You can check the size of the nonce for a database by using the '.dbinfo' command in an ordinarysqlite3.exe command-line shellprogram. The output of the '.dbinfo' command will look something like this:
Bytes 16 through 23 of the database are unencrypted. Thus, you canalways check to see how much nonce is being used, even on an encrypteddatabase file, just by looking at byte 20. It is recommended thatany product that uses encryption check this byte to make sure itis being set to 4 or 12 or 32 and not 0.
10.0 Security Checklist
When using SEE in an application, it is recommended that you double-checkthat everything is implemented correctly, and that you are getting strongencryption, by performing the following tests, at a minimum:
- Use the SEE-enabled CLI to run the 'sqlite3 $DATABASE .dbinfo' command (adding an appropriate -key, -hexkey, or -textkey argument) and verify that your encrypted database files contain a nonce. The nonce should be at least 12 bytes.
- Use the SEE-enabled CLI to read an encrypted database, but change the last character of the supplied key by a single character value. Verify that a minor change to the end of the key like this renders the database unreadable. The error message should be 'file is not a database'. Repeat this test with multiple variations of the key. Confirm that the database is only accessible if the key is exactly correct.
- Try to compress an encrypted database file and verify that the file is uncompressible. In other words, run a program like 'zip' or 'gzip' against the encrypted database and verify that compression does not change the size of the file more than a few bytes smaller.
Limitations
- TEMP tables are not encrypted.
- In-memory (':memory:') databases are not encrypted.
- Bytes 16 through 23 of the database file contain header information which is not encrypted.
11.0 How SEE Works
Each page is encrypted separately. The key to encryption is a combination of the page number, the random nonce (if any) and the database key. The data is encrypted in both the main database andin the rollback journal or WAL file but is unencrypted when held in memory. This means that if an adversary is able to view the memory usedby your program, she will be able to see unencrypted data.
The nonce value is changed by a rollback.
Sqlite Dbeaver Command
The see-aes128-ccm.c variant uses AES in CCM mode with a 16-byte randomly choosen nonce on each page and and 16-byte messageauthentication code (MAC). Thus with crypto3ccm.c, 32 bytesof every database pages are taken up by encryption andauthentication overhead. Consequently, database files createdusing crypto3ccm.c may be a little larger. Also, because theMAC is computed whenever a page is modified, and verified whena page is read, crypto3ccm.c will often be a little slower.Such is the cost of authentication.
Sqlite Dbeaver Database
- Dark theme support was improved (Windows 10 and GTk)
- Data viewer:
- Copy As: format configuration editor was added
- Extra configuration for filter dialog (performance)
- Sort by column as fixed (for small fetch sizes)
- Case-insensitive filters support was added
- Plaintext view now support top/bottom dividers
- Data editor was fixed (when column name conflicts with alias name)
- Duplicate row(s) command was fixed for multiple selected rows
- Edit sub-menu was returned to the context menu
- Columns auto-size configuration was added
- Dictionary viewer was fixed (for read-only connections)
- Current/selected row highlighting support was added (configurable)
- Metadata search now supports search in comments
- GIS/Spatial:
- Map position preserve after tiles change
- Support of geometries with Z and M coordinates was added
- Postgis: DDL for 3D geometry columns was fixed
- Presto + MySQL geometry type support was added
- BigQuery now supports spatial data viewer
- Binary geo json support was improved
- Geometry export was fixed (SRID parameter)
- Tiles definition editor was fixed (multi-line definitions + formatting)
- SQL editor:
- Auto-completion for objects names with spaces inside was fixed
- Database objects hyperlinks rendering was fixed
- SQL Server: MFA (multi-factor authentication) support was added
- PostgreSQL: array data types read was fixed
- Oracle: indexes were added to table DDL
- Vertica: LIMIT clause support was improved
- Athena: extra AWS regions added to connection dialog
- Sybase IQ: server version detection was improved
- SAP ASE: user function loading was fixed
- Informix: cross-database metadata read was fixed
- We migrated to Eclipse 2021-03 platform
